MicroCell is an open-source, MicroVM-based sandbox runtime built for running AI agent tool actions with clear isolation boundaries. Once an agent can execute code, run shell commands, touch files, or call utilities, you need stronger separation than a normal process boundary - without building a full platform to get it. MicroCell solves this by providing a small runtime that spins up an isolated environment, runs a task with controlled permissions and resource limits, captures outputs, and tears the environment down predictably.
Why MicroVMs for Agents
Container-based sandboxes share a kernel with the host and rely on namespace isolation that has known escape vectors. For agent workloads - where the code being executed is generated or selected by an LLM — the threat model is different from typical containerized services. MicroCell uses lightweight virtual machines to provide a hardware-enforced isolation boundary: each task runs in its own VM with its own kernel, so a compromised workload cannot reach the host or other tasks.
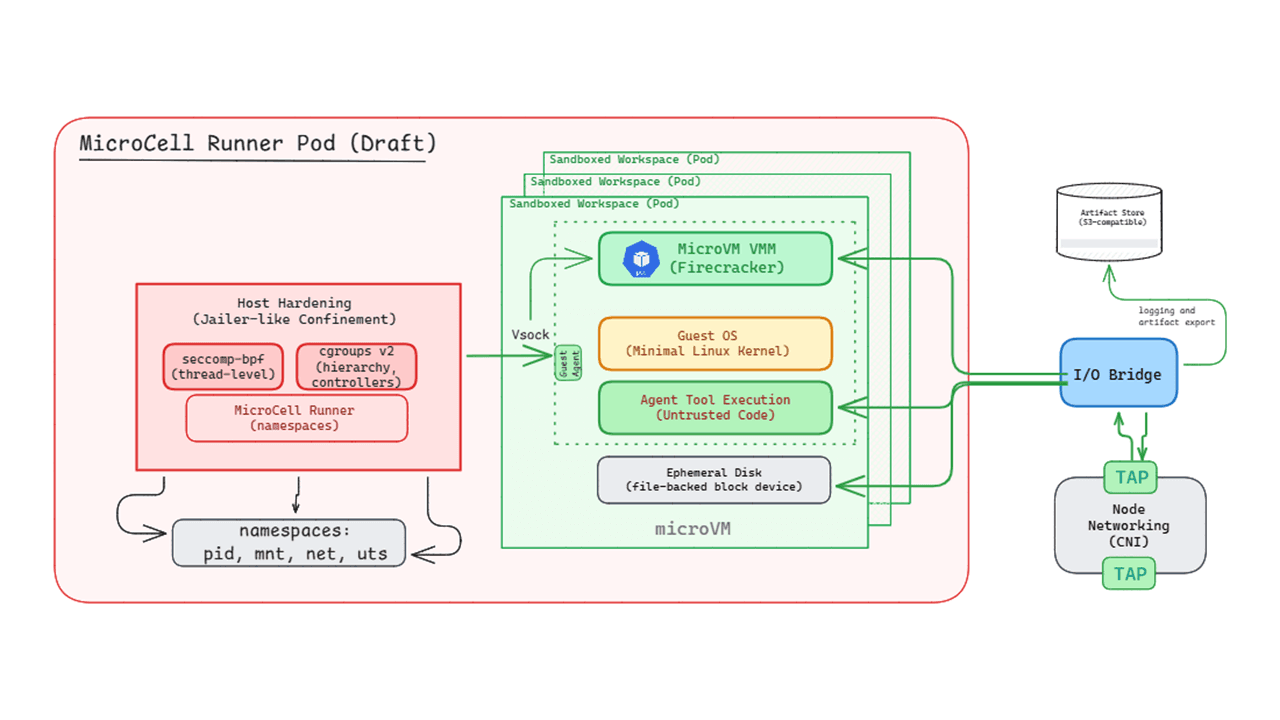
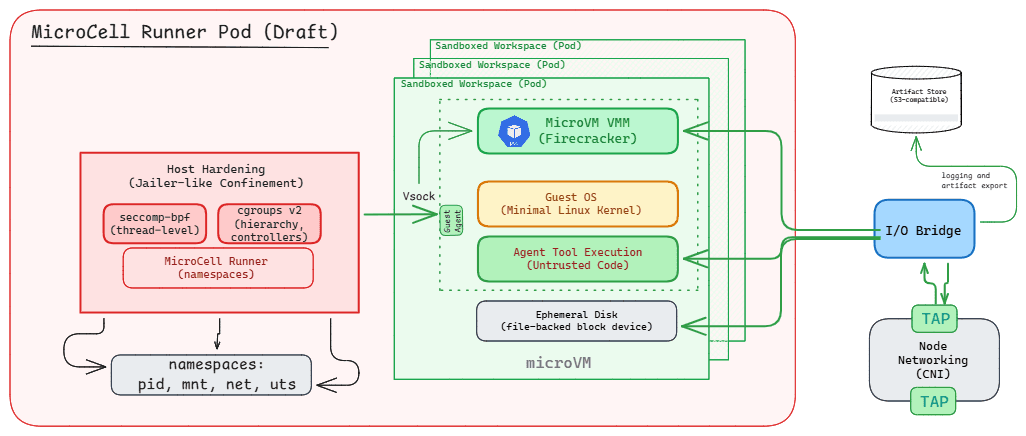
Architecture
Controller: Receives a tool request, validates it against policy, and orchestrates the full execution lifecycle.
MicroVM Runner: Provisions an isolated VM instance with sub-second cold starts. Attaches required resources (filesystem mounts, environment variables, network rules) and enforces CPU/memory/time limits.
I/O Bridge: Handles input injection (files, environment) and output collection (stdout/stderr streaming, artifact export). Provides real-time log streaming so the calling agent can observe execution as it happens.
Policy & Limits: Enforces resource quotas, allowed commands, network access rules, and execution timeouts. The policy surface is explicit and auditable.
Cleanup: Guarantees consistent teardown after every execution - no state leaks between tasks, no orphaned resources.
Design Principles
Minimal surface area: Keep the runtime small so the trust boundary and assumptions remain obvious and auditable.
Clean lifecycle: Create → execute → collect outputs → destroy, with predictable cleanup at every stage.
Framework-agnostic: No assumption of a specific agent framework - MicroCell provides execution isolation as a service that any orchestrator can call.
Resource-bounded: CPU, memory, time, and I/O limits are enforced at the VM level, preventing runaway tasks from affecting the host or other workloads.
Scope
MicroCell focuses on secure execution boundaries for agent tools. It is intentionally minimal: no multi-tenant scheduler, no heavy orchestration layer, and no coupling to specific agent frameworks. The goal is a reliable, auditable execution primitive that agentic systems can build on top of.
MicroCell is being developed as a standalone OSS project. The GitHub repository will be published soon.